Know the Signal, Trust the Signal
I’ve been doing a lot of traveling and speaking about Microsoft security products. One of the areas I like to talk about is alerting from the Office 365 Protection Center and Cloud App Security. The talking point goes that Microsoft relies on alerts generated within Cloud App Security to predict, with a high degree of accuracy, when someone is preparing to leave the organization.
There are a number of metrics that can be enabled for alerting, like suspicious logins, activity from anonymous IP’s, and impossible travel events, but there are a pair of canned alert policies in CAS that, when triggered together, generally add up to “job hunting:”
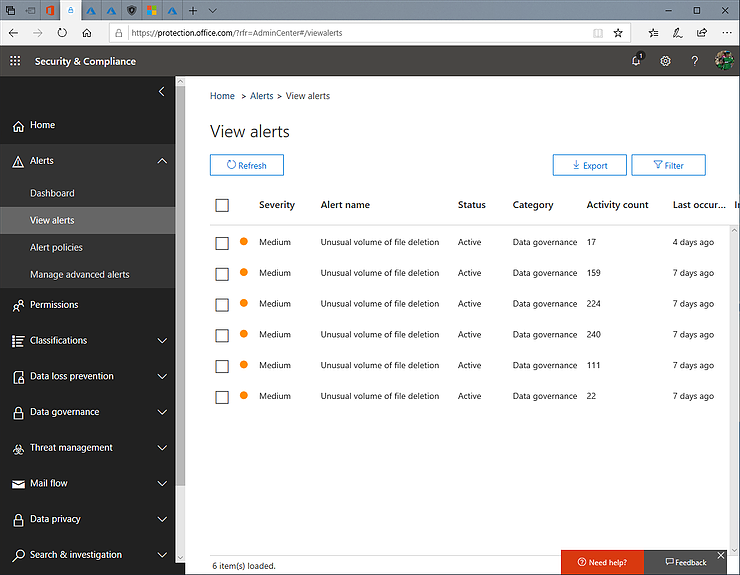
A little poking revealed that these were all one user, and guess what: that user just tendered their resignation. What I found particularly useful was that this was all 100% pre-canned reporting. The client had done nothing at all to enable it: it’s a default policy.
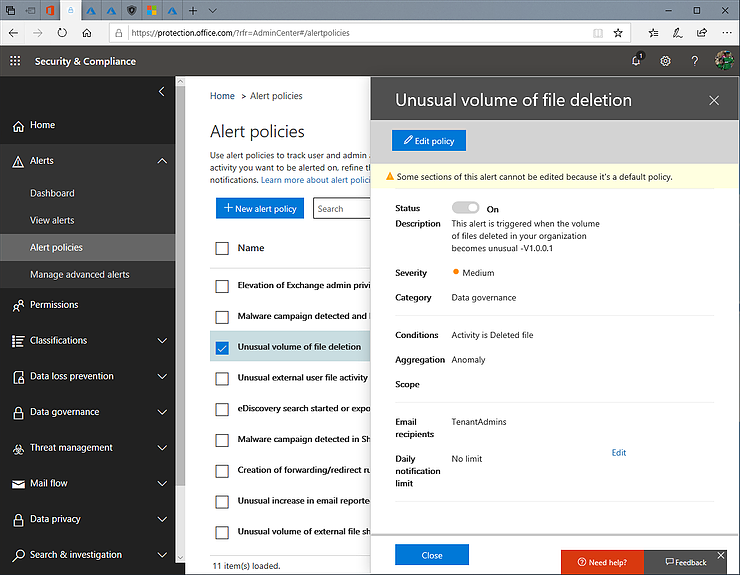
So the signal was there, and the signal was correct: the user was planning to depart. And though it was only detected after the resignation was tendered, this organization now knows how to correlate the data to protect themselves from future staffing challenges!


Comments